The dark web is an enigmatic and often misunderstood part of the internet, housing both illicit activities and unique opportunities for privacy and expression. This blog delves into the complexities of the dark web, its history, how it operates, and the dual nature of its offerings.
The internet has revolutionized our world, transforming how we work, play, and live. It’s a vast digital realm with something for everyone, regardless of interests or beliefs.
The internet has connected us in unprecedented ways. It’s a virtual meeting place where people from all corners of the globe can come together, share ideas, and find like-minded individuals.
The Internet’s Vastness
- Over 1,000 photos posted on Instagram every second
- 8,000 tweets posted on Twitter every second
- 70,000 Google searches occur every second
- Nearly 100,000 YouTube videos watched every second
The internet offers an abundance of options. Whether you’re seeking services, products, or information – legal or otherwise – it’s all available online. This power comes with responsibility, as users can choose to use it for good or bad.
Understanding the Surface Web
The surface web is the part of the internet most people interact with daily. It’s easily accessible and indexed by search engines like Google.
- Includes popular social media platforms
- Easily searchable content
- Public information readily available
- High volume of daily traffic
While the surface web seems vast, it has its boundaries. Sensitive information like bank accounts and medical records are not freely accessible here. These are protected behind passwords, leading us into the realm of the Deep Web.
What is the Deep Web?
The Deep Web is a vast, often misunderstood part of the internet. It’s much larger than most people realize, encompassing a significant portion of our online world.
Contrary to popular belief, the Deep Web isn’t a mysterious or dangerous place. It’s simply the part of the internet that isn’t indexed by search engines.
- Includes password-protected content
- Contains private databases and intranets
- Comprises 96% of the entire internet
- Includes everyday services like email
You might be surprised to learn that you’ve likely used the Deep Web today. Logging into your email account or accessing your online banking are examples of Deep Web activities.
The sheer size of the Deep Web is staggering. It’s so vast that even if you browsed new websites every day for 50 years, you’d barely scratch the surface of what’s available.
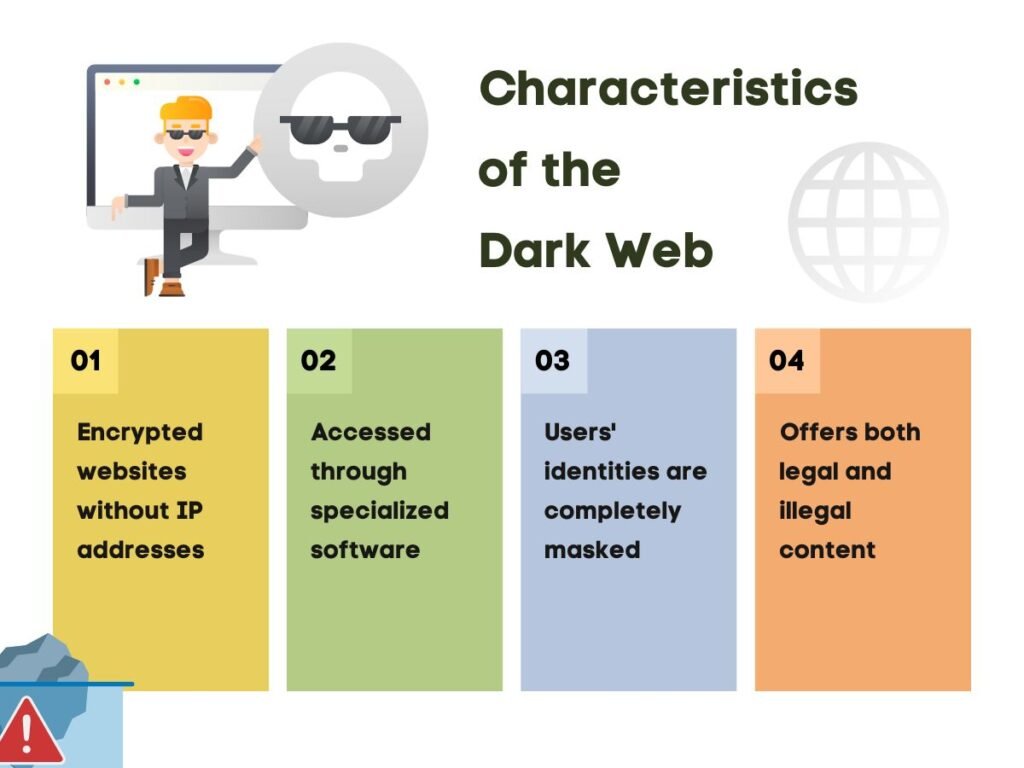
Beyond the Deep Web lies an even more secretive realm: the Dark Web. This tiny fraction of the internet is where anonymity reigns supreme and conventional rules often don’t apply.
The Origins of Dark Web Technology: Onion Routing
The dark web is a hidden segment of the internet that is not indexed by traditional search engines and requires special tools to access. Its origins are deeply rooted in government initiatives aimed at protecting privacy and facilitating secure communications. Here’s a detailed overview of the dark web’s origin:
Onion Routing protects data by wrapping it in multiple layers of encryption. Tor, which stands for “The Onion Router,” is the most well-known implementation of Onion Routing.
The concept that eventually led to the dark web began in the mid-1990s with the development of Onion Routing. This technology was created by researchers at the U.S. Naval Research Laboratory, including Paul Syverson, David Goldschlag, and Michael Reed. The primary goal was to enable secure communications for U.S. intelligence personnel. Onion Routing allows users to send data anonymously over the internet by encrypting it in multiple layers, similar to the layers of an onion. Each relay in the network only knows the previous and next point in the transmission chain, ensuring that the original sender remains anonymous.
Here’s a simplified breakdown of how it operates:
- Final Decryption: When the message reaches the last node, known as the exit node, it is fully decrypted and sent to its final destination. To anyone monitoring the network, it appears as if the message originated from the exit node rather than the actual sender
- Multiple Layers of Encryption: When a user sends a message, it is wrapped in several layers of encryption. Each layer is decrypted by a different node (or relay) in the network.
- Relay Nodes: The message travels through a series of randomly selected nodes. Each node only knows the location of the previous and next node, thereby obscuring the origin and destination of the message. This means that no single node can see both the sender and the recipient.
Patent and Transition to Public Use
In 1998, the U.S. Navy patented Onion Routing, and its development continued under the Defense Advanced Research Projects Agency (DARPA). By 2002, the technology evolved into the Tor Project (The Onion Router), which was established to further develop and maintain the software. The Tor Project was created by a group of computer scientists who believed in the importance of privacy and anonymity on the internet. The Navy later released the Tor software as open-source, allowing anyone to use it.
The development of Dark Web technology reflects increasing concerns about online privacy. While some individuals view data tracking as a benign practice, others perceive it as a significant invasion of personal privacy. The Dark Web, accessed primarily through the Tor network, offers a platform where users can maintain anonymity, which can be beneficial for those in oppressive regimes or for whistleblowers. However, this same anonymity also facilitates illegal activities, such as the trafficking of drugs and weapons, highlighting the dual-edged nature of privacy in the digital age.
In summary, Onion Routing, the foundational technology of the Dark Web, was designed to protect sensitive communications but has evolved into a tool for both privacy and illicit activities. The ongoing debate around online privacy underscores the complexity of navigating these technologies in today’s digital landscape.
Growth and Expansion: 2000s Onwards
Rise of the Tor Network
After its release, the Tor network gained popularity among various groups, including privacy advocates, journalists, and individuals living under oppressive regimes. It provided a means to communicate and share information without fear of censorship or surveillance. The Tor network became a crucial tool for whistleblowers and activists seeking to protect their identities.
Emergence of the Dark Web
As the Tor network expanded, it facilitated the creation of websites that operated anonymously, leading to the emergence of the dark web. Unlike the deep web, which contains non-indexed content like databases and private accounts, the dark web consists specifically of sites that require Tor for access and often engage in illicit activities. The term “dark web” began to gain traction in the late 2000s, particularly as awareness grew about its use for illegal transactions.
Accessing the Dark Web: Tools and Techniques
Entering the Dark Web requires specific tools and knowledge. While it may seem daunting, the process is relatively straightforward for those who know what they’re doing.
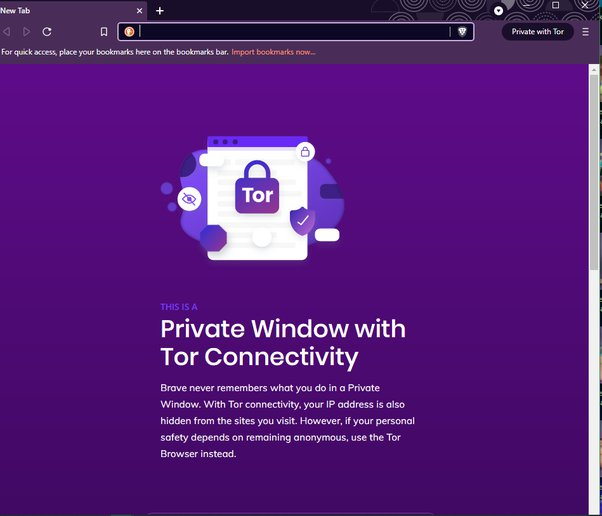
The Tor Browser
The Tor browser is the primary tool for accessing the Dark Web. Here’s what you need to know about it:
Appearance: The Tor browser looks and functions like a standard web browser (such as Chrome or Firefox), making it user-friendly.
Access to .onion Sites: It allows users to visit websites with .onion domains, which are exclusive to the Dark Web. These sites cannot be accessed through regular browsers.
Anonymity: One of the main features of the Tor browser is its ability to conceal the user’s identity and location. It routes internet traffic through multiple servers, making it difficult to trace back to the user.
Navigating the Dark Web is different from browsing the regular internet. Here’s how it works:
Unique Links: Dark Web links are not like standard URLs. Instead of familiar domain names (like www.example.com), they consist of random strings of characters and always end with .onion. This adds another layer of anonymity and security.
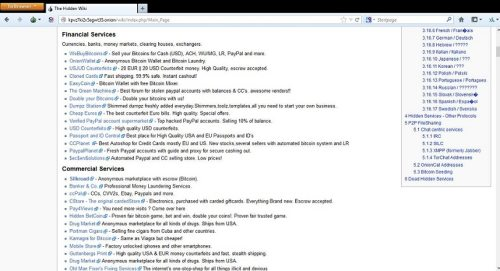
A useful resource for those exploring the Dark Web is the Hidden Wiki:
Directory of Services: The Hidden Wiki serves as a directory that lists various Dark Web services, both legal and illegal. It can help users find specific sites and resources.
Starting Point: For newcomers, the Hidden Wiki is often a good starting point to understand what’s available on the Dark Web and to navigate its complexities.

Cryptocurrencies and Transactions
To maintain anonymity while making transactions on the Dark Web, users typically rely on cryptocurrencies:
Bitcoin and Privacy: Cryptocurrencies like Bitcoin are commonly used because they offer a level of privacy that traditional payment methods (like credit cards) do not. Transactions made with Bitcoin do not directly link to a user’s identity.
Bitcoin Wallets: Users need a Bitcoin wallet to store their cryptocurrencies, which allows them to make anonymous transactions without revealing personal information.
Marketplace Operations: Cryptocurrencies are essential for conducting business on Dark Web marketplaces, where anonymity is crucial for both buyers and sellers.
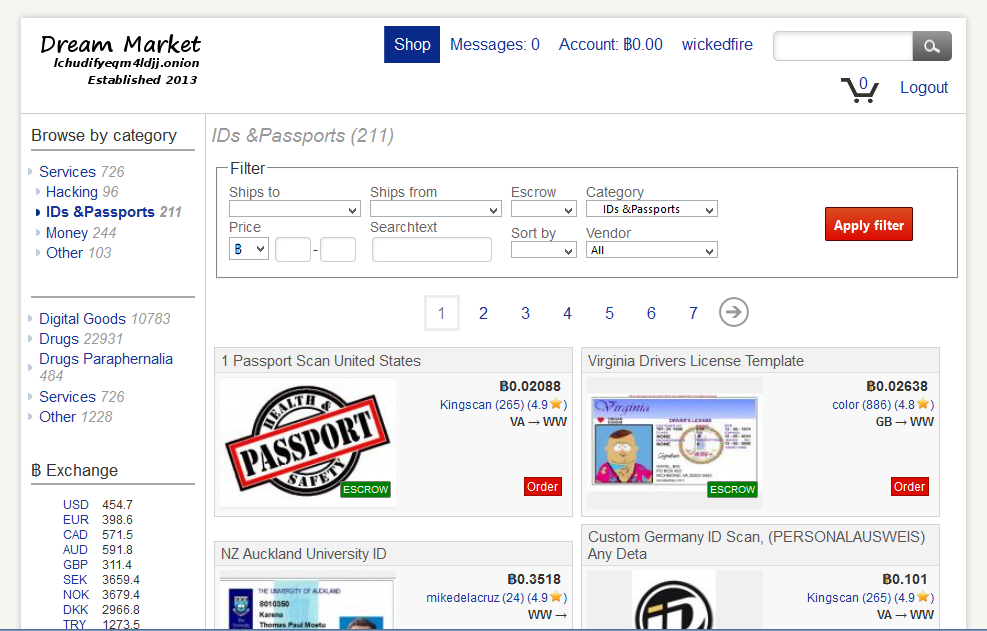
Dark Web Marketplaces
Dark Web marketplaces are platforms where various goods and services are offered:
Variety of Offerings: These marketplaces can sell anything from legal items to illegal goods, including drugs and hacking services. The infamous Silk Road was one of the first and most well-known Dark Web marketplaces, although it has since been shut down.
Anonymity in Transactions: These marketplaces rely on the anonymity provided by the Tor browser and cryptocurrencies to facilitate transactions without exposing the identities of the users involved.
While it can be a space for anonymity and privacy, it also contains risks and illegal activities, making it essential to approach with caution and awareness.
The Silk Road and Its Legacy
The Silk Road, a notorious dark web marketplace, left an indelible mark on the internet’s underbelly. Its impact extends far beyond its brief existence, influencing cryptocurrency adoption and shaping the landscape of online black markets.
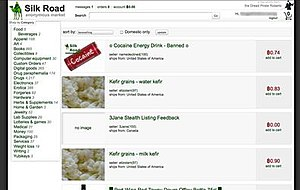
The Rise of Silk Road
The Silk Road was a pioneering online marketplace that operated on the dark web, known for facilitating the sale of illegal goods and services. Launched in 2011 by Ross Ulbricht under the pseudonym “Dread Pirate Roberts,” Silk Road became a symbol of the dark web’s potential for anonymity and illicit commerce.

Its legacy continues to influence the landscape of online marketplaces and discussions about internet privacy and regulation. Here are the key factors:
- Created in 2011
- Utilized Bitcoin for transactions
- Offered various illegal goods and services
- Operated for approximately two years
Economic Impact of the Silk Road on the Dark Web
The Silk Road on the dark web, which operated from 2011 until its shutdown in 2013, was a significant online marketplace that facilitated the trade of illegal goods and services, primarily drugs. Its economic impact can be analyzed from various angles, including its influence on the dark web economy, the broader implications for online commerce, and the lessons learned regarding regulation and law enforcement. Below is a detailed examination of the economic impact of the Silk Road on the dark web.
1. Creation of a New Marketplace Economy
The Silk Road established a pioneering model for online marketplaces that operated under the principles of anonymity and decentralized transactions:
- Anonymity and Security: By utilizing the Tor network and cryptocurrencies like Bitcoin, Silk Road allowed users to conduct transactions without revealing their identities. This model attracted a significant number of users seeking to buy or sell illegal goods, thereby creating a thriving underground economy.
- Diverse Product Offerings: The marketplace offered a wide range of products, including drugs, counterfeit documents, hacking tools, and more. This diversity not only catered to various consumer needs but also encouraged competition among sellers, impacting pricing and product availability.
2. Influence on Subsequent Dark Web Marketplaces
Silk Road’s success inspired the emergence of numerous other dark web marketplaces:
- Legacy of Marketplaces: After the shutdown of Silk Road, other platforms such as Silk Road 2.0 and AlphaBay emerged, replicating its business model. This continuity demonstrated the demand for anonymous online trade and solidified the concept of dark web marketplaces as a viable economic sector.
- Market Dynamics: The proliferation of these marketplaces led to increased competition, which affected pricing strategies and the range of products available. Sellers had to adapt to consumer preferences and market trends, similar to legitimate online marketplaces.
3. Economic Consequences of Law Enforcement Actions
The closure of Silk Road and subsequent law enforcement actions had significant economic implications for the dark web:
- Market Disruption: The shutdown of Silk Road created a temporary vacuum in the dark web marketplace. While new platforms quickly emerged, the disruption highlighted the fragility and volatility of the dark web economy.
- Increased Security Measures: Following the crackdown, many dark web marketplaces implemented enhanced security measures to protect against law enforcement. This included more sophisticated encryption and the use of privacy-focused cryptocurrencies, which further shaped the economic landscape of the dark web.
4. Impact on Cryptocurrency Adoption
Silk Road played a crucial role in popularizing cryptocurrencies, particularly Bitcoin:
- Bitcoin as a Currency: The use of Bitcoin for transactions on Silk Road demonstrated the potential for cryptocurrencies to facilitate anonymous trade. This not only boosted Bitcoin’s adoption but also influenced the development of other cryptocurrencies aimed at enhancing privacy.
- Market Volatility: The association of Bitcoin with illegal activities led to fluctuations in its value, impacting the broader cryptocurrency market. The Silk Road phenomenon contributed to discussions about the legitimacy and regulation of cryptocurrencies.
5. Economic Lessons and Regulatory Challenges
The existence of Silk Road and its successors raised important questions about regulation and the challenges of governing online marketplaces:
- Regulatory Responses: The Silk Road highlighted the difficulties law enforcement faced in regulating the dark web. The need for effective strategies to combat illegal online activities became a significant focus for governments worldwide.
- Balancing Privacy and Security: The Silk Road’s legacy continues to influence debates on privacy, freedom of expression, and the regulation of online spaces. Policymakers grapple with the challenge of ensuring security while respecting individual privacy rights.
The Fall of The Silk Road and Aftermath
The rise of Silk Road did not go unnoticed by law enforcement agencies. The FBI and other agencies began investigating the marketplace, focusing on identifying its operators and users. They employed various techniques, including monitoring transactions and tracking Bitcoin movements.
On October 1, 2013, the FBI arrested Ross Ulbricht in a San Francisco public library. At the time of his arrest, Ulbricht was logged into the Silk Road site, and authorities seized his laptop, which contained critical evidence linking him to the operation of the marketplace. The FBI also shut down Silk Road, effectively dismantling one of the largest online drug markets at the time.
In 2015, Ulbricht was convicted on multiple charges, including:
- Conspiracy to commit money laundering
- Conspiracy to commit computer hacking
- Conspiracy to traffic narcotics
- Engaging in a continuing criminal enterprise
He was sentenced to life in prison without the possibility of parole. Ulbricht’s defense argued that he was not directly involved in selling drugs but rather created a platform for others to do so. However, the jury found him guilty, emphasizing the impact of Silk Road on illegal drug trade.
Ross Ulbricht’s Incarceration and Appeals
Since his conviction, Ulbricht has remained incarcerated at the United States Penitentiary in Tucson. His family and supporters have campaigned for his release, arguing that his life sentence is disproportionate to his crimes. Ulbricht’s appeals to higher courts have been unsuccessful, but discussions about his case continue to resonate in conversations about justice and reform in drug policy.
Ethical Dilemmas and Dark Transactions
The dark web presents a complex landscape filled with ethical dilemmas and illicit activities. While it offers users anonymity and freedom from censorship, it also serves as a platform for some of the most disturbing aspects of human behavior. Here’s a detailed key factors of the ethical dilemmas and dark transactions associated with the dark web.
Anonymity and Ethical Dilemmas
The Double-Edged Sword of Anonymity
Anonymity is one of the primary features of the dark web, facilitated by technologies like the Tor network. While it protects users from surveillance and censorship, it also enables unethical behavior:
Freedom of Expression vs. Harmful Content: Anonymity allows individuals to express dissenting opinions in oppressive regimes. However, it also provides a shield for those engaging in illegal activities, such as trafficking drugs, weapons, and even human beings. This creates a moral dilemma: how to balance the right to free speech with the potential for harm.
Protection of Whistleblowers vs. Criminal Activity: The dark web can serve as a refuge for whistleblowers who expose corruption or wrongdoing. Yet, the same environment also harbors cybercriminals, leading to a complex ethical landscape where the same tools can be used for both good and ill.
Disturbing Content and Exploitation
The dark web is notorious for hosting disturbing content, including:
Child Exploitation: One of the most egregious ethical dilemmas is the presence of child pornography and exploitation rings. These activities raise profound moral questions about the responsibilities of law enforcement and the platforms that host such content.
Hate Speech and Extremism: The dark web also facilitates the spread of hate speech and extremist ideologies. This raises concerns about the impact of anonymity on societal norms and the potential for radicalization.
Dark Transactions and Their Implications
Illicit Markets
The dark web is home to numerous illicit markets where illegal goods and services are traded:
Drug Trafficking: Silk Road was one of the first and most well-known dark web marketplaces, facilitating the sale of illegal drugs. The ease of access and anonymity provided by such platforms has led to increased drug trafficking, raising questions about public health and safety.
Weapons and Human Trafficking: Beyond drugs, the dark web also facilitates the trade of weapons and human trafficking. These transactions pose significant ethical challenges regarding the responsibilities of governments and law enforcement agencies to protect vulnerable populations.
Economic Impact
The economic implications of dark transactions are significant:
Impact on Local Economies: The proliferation of dark web markets can undermine local economies by facilitating the illegal drug trade, which often leads to increased crime rates and social instability.
Cryptocurrency and Financial Crime: The use of cryptocurrencies for transactions on the dark web complicates efforts to trace and regulate financial activities. This raises ethical questions about the role of cryptocurrency in facilitating illegal activities while also providing legitimate users with privacy.
Conclusion: The Future of the Dark Web
The dark web’s future remains uncertain, balancing privacy concerns with illegal activities. Its evolution will likely depend on technological advancements, legal frameworks, and society’s changing attitudes towards online anonymity.
Ongoing Challenges: Law Enforcement and Ethical Challenges
As technology evolves, the dark web will continue to adapt. Law enforcement and cybersecurity experts will face new challenges in combating illicit activities while preserving legitimate uses for privacy and free speech.
Policing the Dark Web
Law enforcement agencies face significant challenges in policing the dark web:
Balancing Privacy and Security: The need to protect civil liberties while combating illegal activities creates a complex ethical landscape. Law enforcement must navigate the fine line between surveillance for safety and the right to privacy.
Effectiveness of Digital Policing: The anonymous nature of the dark web makes it difficult for law enforcement to gather intelligence and effectively combat crime. This raises ethical questions about the methods used in digital policing and the potential for overreach.
Ethical Considerations in Research
Researchers studying the dark web also encounter ethical dilemmas:
Data Collection and Privacy: Gathering data from the dark web can involve ethical concerns regarding user privacy and consent. Researchers must navigate the complexities of studying a space designed for anonymity while respecting the rights of individuals.
Potential for Harm: Engaging with dark web content can expose researchers to disturbing material, raising questions about the psychological impact of such research and the responsibilities of researchers to protect themselves and their subjects.
Secure Your Digital Environment: The First Step Against Cyber Threats
In today’s digital age, ensuring a secure online environment is paramount to protecting yourself from malware and cybersecurity threats. The first step in safeguarding your personal information and online activities is to establish a secure digital environment. One effective way to enhance your online security is by using a reliable VPN (Virtual Private Network).
If you’re considering a good VPN, we recommend NordVPN for the following reasons:
- Robust Security Features: NordVPN employs advanced encryption protocols that protect your data from hackers and cybercriminals, ensuring your online activities remain private.
- No-Logs Policy: With a strict no-logs policy, NordVPN guarantees that your browsing history is not stored or monitored, providing you with peace of mind while you surf the web.
- Global Server Coverage: NordVPN offers a vast network of servers around the world, allowing you to bypass geo-restrictions and access content securely from anywhere.
Taking the necessary steps to secure your digital environment is crucial in today’s interconnected world. Click the button below to learn more about how NordVPN can help you enhance your online security.